基于eNSP中大型校园/企业网络规划与设计_综合大作业
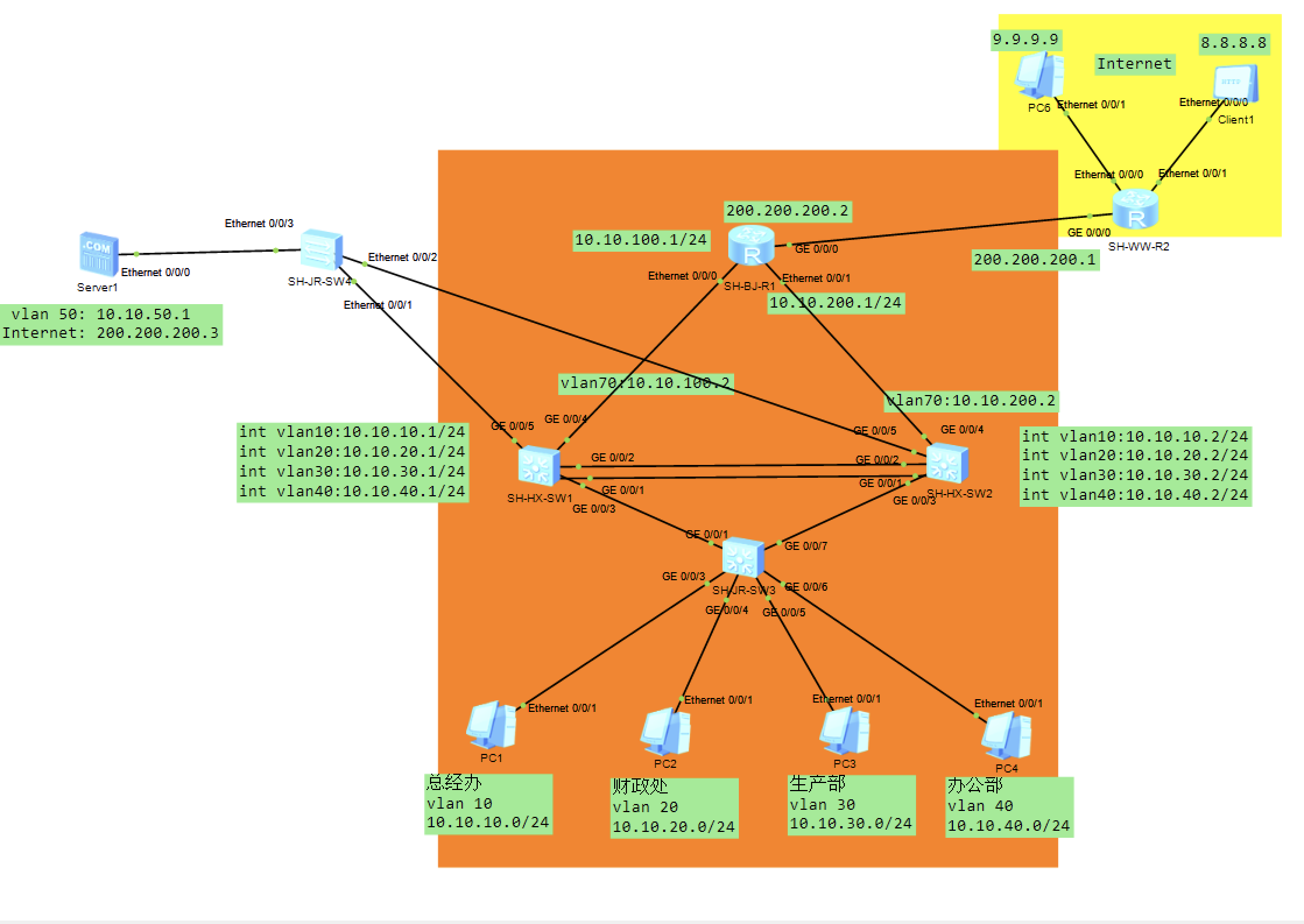
topo图
需求说明 1、总部局域网中所有业务IP地址参考IP地址规划表。
2、局域网使用VLAN 技术进行业务二层隔离,不同业务部门划分到不同的VLAN;其中总部主要业务分别有总经办PC1(vlan10)、财务部PC2(vlan20)、生产部PC3(vlan30)、办公部PC4(vlan40)和服务器区(vlan50)。
3、为了保证核心层链路高可靠性,总部核心交换机SH-HX-SW1和SH-HX-SW2之间,使用eth-trunk来做链路聚合,手工负载均衡方式;
4、总部接入层交换机和核心交换机之间运行MSTP,杜绝二层环路,其中SH-HX-SW1为VLAN10、VLAN20的根网桥,作为VLAN30、VLAN40和VLAN50的备份根;SH-HX-SW2为VLAN30、VLAN40和VLAN50的根网桥,作为VLAN10、VLAN20的备份根;
5、为保障网关的高可靠性,总部采用双核心设计架构,SH-HX-SW1和SH-HX-SW2为VRRP主备网关,提供网关冗余并且实现流量的负载均衡,VLAN10、VLAN20的主网关为SH-HX-SW1,备份网关为SH-HX-SW2。 VLAN30、VLAN40和VLAN50主网关为SH-HX-SW2,备份网关为SH-HX-SW1,具体地址配置请参照IP地址分配表;
6、总部局域网内实现流量互通,采用动态路由协议OSPF协议进行业务互访,具体配置根据实际情况而定。
7、总部核心交换机SH-HX-SW1和SH-HX-SW2做DHCP Server,为总部用户动态分配IP地址,两个核心交换机DHCP服务器互做备份。
8、公司内部有流量访问控制需求:
(1)总经理办公室可以访问公司内部所有业务;
(2)总部生产部和办公部不允许相互访问,但是均可以访问总经办和WEB服务器区域,不允许访问其他部门;
(3)财务部只允许访问总经办和服务器,其他部门均不允许访问。
9、Internet访问需求:
(1)企业总部为了保证Internet访问,申请了电信宽带。其中SH-BJ-R1连接电信出口。
(2)企业向电信运营商申请了一个公网地址 200.200.200.2,用于公网接口并且内部用户上网(Easy IP);同时申请一个公网地址200.200.200.3,用于将内网的服务器发布到Internet中,并且允许 Internet 中主机可以访问内部WEB服务器(静态NAT);
(3)总部总经办、办公部和服务器可以访问Internet,财务部和生产部不允许访问Internet。
(4)Internet部分用一个路由器来进行模拟,Internet部分对应接口地址直接参考地址规划表。
1.IP规划+VLAN规划 原理:
VLAN(Virtual Local Area Network)即虚拟局域网,是一种将物理的LAN在逻辑上划分为多个广播域的通信技术。每一个VLAN都是一个广播域,VLAN内的主机可以直接通信,而不同VLAN之间则不能通信。
VLAN作用:
限制广播域(广播域被限制在VLAN之中,降低带宽,提高网络处理能力)
增强局域网安全(不同VLAN内的报文在传输时相互隔离,即一个VLAN内的用户不能和其它VLAN内的用户直接通信。)
提高网络健壮性(不同VLAN之间不会相互影响)
SH-HX-SW1 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 SH - HX - SW1 :< Huawei > sys[Huawei ]un in en [Huawei ]sysname SH - HX - SW1 # 创建VLAN [SH - HX - SW1 ]vlan 10 description ZJB vlan 20 description CZC vlan 30 description SCB vlan 40 description BGB vlan 50 description WEB # 三层交换机接口配置IP地址 [SH - HX - SW1 ]interface Vlanif10 ip address 10.10 .10.1 255.255 .255.0 interface Vlanif20 ip address 10.10 .20.1 255.255 .255.0 interface Vlanif30 ip address 10.10 .30.1 255.255 .255.0 interface Vlanif40 ip address 10.10 .40.1 255.255 .255.0 interface Vlanif50 ip address 10.10 .50.1 255.255 .255.0 # 配置trunk [SH - HX - SW1 ]interface GigabitEthernet0 / 0 / 3 port link- type trunk port trunk allow- pass vlan all interface GigabitEthernet0 / 0 / 5 port link- type trunk port trunk allow- pass vlan all
SH-HX-SW2 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 SH - HX - SW2 :< Huawei > sys[Huawei ]un in en [Huawei ]sysname SH - HX - SW2 # 创建VLAN [SH - HX - SW2 ]vlan 10 description ZJB vlan 20 description CZC vlan 30 description SCB vlan 40 description BGB vlan 50 description WEB # 三层交换机接口配置IP地址 [SH - HX - SW2 ]interface Vlanif10 ip address 10.10 .10.2 255.255 .255.0 interface Vlanif20 ip address 10.10 .20.2 255.255 .255.0 interface Vlanif30 ip address 10.10 .30.2 255.255 .255.0 interface Vlanif40 ip address 10.10 .40.2 255.255 .255.0 interface Vlanif50 ip address 10.10 .50.2 255.255 .255.0 # 配置trunk [SH - HX - SW2 ]interface GigabitEthernet0 / 0 / 3 port link- type trunk port trunk allow- pass vlan all interface GigabitEthernet0 / 0 / 5 port link- type trunk port trunk allow- pass vlan all
SH-HX-SW3 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 SH - JR - SW3 :< Huawei > sys[Huawei ]un in en [Huawei ]sysname SH - HX - SW3 # 创建VLAN [SH - HX - SW3 ]vlan 10 description ZJB vlan 20 description CZC vlan 30 description SCB vlan 40 description BGB # 划分VLAN [SH - HX - SW3 ]interface GigabitEthernet0 / 0 / 3 port link- type access port default vlan 10 # interface GigabitEthernet0 / 0 / 4 port link- type access port default vlan 20 # interface GigabitEthernet0 / 0 / 5 port link- type access port default vlan 30 # interface GigabitEthernet0 / 0 / 6 port link- type access port default vlan 40 # 配置trunk [SH - HX - SW3 ]interface GigabitEthernet0 / 0 / 1 port link- type trunk port trunk allow- pass vlan all interface GigabitEthernet0 / 0 / 7 port link- type trunk port trunk allow- pass vlan all
PC 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 # PC配置静态地址 PC1 IP : 10.10 .10.10 Subnet mask: 255.255 .255.0 Gateway : 10.10 .10.254 PC2 IP : 10.10 .20.10 Subnet mask: 255.255 .255.0 Gateway : 10.10 .20.254 PC3 IP : 10.10 .30.10 Subnet mask: 255.255 .255.0 Gateway : 10.10 .30.254 PC4 IP : 10.10 .40.10 Subnet mask: 255.255 .255.0 Gateway : 10.10 .40.254
2.链路聚合 链路聚合是将物理接口捆绑在一起作为一个逻辑接口来增加带宽和可靠性的方法。将若干条以太链路捆绑在一起形成的逻辑链路,简写为Eth-Trunk.
作用:增加带宽、提供冗余、分担负载、节约成本等
SW1 1 2 3 4 5 6 7 8 9 [SH - HX - SW1 ]interface Eth - Trunk 1 mode lacp- static port link- type trunk port trunk allow- pass vlan all [SH - HX - SW1 ]interface GigabitEthernet0 / 0 / 1 eth- trunk 1 interface GigabitEthernet0 / 0 / 2 eth- trunk 1
SW2 1 2 3 4 5 6 7 8 9 [SH - HX - SW2 ]interface Eth - Trunk 1 mode lacp- static port link- type trunk port trunk allow- pass vlan all [SH - HX - SW2 ]interface GigabitEthernet0 / 0 / 1 eth- trunk 1 interface GigabitEthernet0 / 0 / 2 eth- trunk 1
3.生成树MSTP 多生成树协议MSTP(Multiple Spanning Tree Protocol)是IEEE 802.1s中定义的生成树协议,通过生成多个生成树,来解决以太网环路问题。
作用:防止二层环路与链路冗余。基于VLAN的数据负载分担。
SW1 1 2 3 4 5 6 7 8 [SH - HX - SW1 ]stp region- configuration region- name mstp instance 1 vlan 10 20 instance 2 vlan 30 40 50 active region- configuration [SH - HX - SW1 ]stp instance 1 root primary stp instance 2 root secondary
SW2 1 2 3 4 5 6 7 8 [SH - HX - SW2 ]stp region- configuration region- name mstp instance 1 vlan 10 20 instance 2 vlan 30 40 50 active region- configuration [SH - HX - SW2 ]stp instance 1 root secondary stp instance 2 root primary
SW3 1 2 3 4 5 [SH - HX - SW3 ]stp region- configuration region- name mstp instance 1 vlan 10 20 instance 2 vlan 30 40 50 active region- configuration
4.VRRP 虚拟路由冗余协议(Virtual Router Redundancy Protocol)是由IETF提出的解决局域网中配置静态网关出现单点失效现象的路由协议,1998年已推出正式的RFC2338协议标准。
作用:
1. 主路由器失效后,备份路由器立即顶替主路由器的工作,保证数据的不丢失。
2.两个不同的路由器成为不同组的主路由器,相互备份。
3.跟踪上行链路接口状态,当上行链路接口失效时,自动将备份路由份提升为主路由器,保证数据的不丢失。
SW1 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 [SH - HX - SW1 ]interface Vlanif10 ip address 10.10 .10.1 255.255 .255.0 vrrp vrid 10 virtual- ip 10.10 .10.254 vrrp vrid 10 priority 110 vrrp vrid 10 preempt- mode timer delay 6 vrrp vrid 10 track interface GigabitEthernet0 / 0 / 3 reduced 30 # interface Vlanif20 ip address 10.10 .20.1 255.255 .255.0 vrrp vrid 20 virtual- ip 10.10 .20.254 vrrp vrid 20 priority 110 vrrp vrid 20 preempt- mode timer delay 6 vrrp vrid 20 track interface GigabitEthernet0 / 0 / 3 reduced 30 # interface Vlanif30 ip address 10.10 .30.1 255.255 .255.0 vrrp vrid 30 virtual- ip 10.10 .30.254 # interface Vlanif40 ip address 10.10 .40.1 255.255 .255.0 vrrp vrid 40 virtual- ip 10.10 .40.254 # interface Vlanif50 ip address 10.10 .50.1 255.255 .255.0 vrrp vrid 50 virtual- ip 10.10 .50.254
SW2 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 [SH - HX - SW2 ]interface Vlanif10 ip address 10.10 .10.2 255.255 .255.0 vrrp vrid 10 virtual- ip 10.10 .10.254 # interface Vlanif20 ip address 10.10 .20.2 255.255 .255.0 vrrp vrid 20 virtual- ip 10.10 .20.254 # interface Vlanif30 ip address 10.10 .30.2 255.255 .255.0 vrrp vrid 30 virtual- ip 10.10 .30.254 vrrp vrid 30 priority 110 vrrp vrid 30 preempt- mode timer delay 6 vrrp vrid 30 track interface GigabitEthernet0 / 0 / 3 reduced 30 # interface Vlanif40 ip address 10.10 .40.2 255.255 .255.0 vrrp vrid 40 virtual- ip 10.10 .40.254 vrrp vrid 40 priority 110 vrrp vrid 40 preempt- mode timer delay 6 vrrp vrid 40 track interface GigabitEthernet0 / 0 / 3 reduced 30 # interface Vlanif50 ip address 10.10 .50.2 255.255 .255.0 vrrp vrid 50 virtual- ip 10.10 .50.254 vrrp vrid 50 priority 110 vrrp vrid 50 preempt- mode timer delay 6 vrrp vrid 50 track interface GigabitEthernet0 / 0 / 5 reduced 30
5.DHCP DHCP(Dynamic Host Configuration Protocol),动态主机配置协议,是一个应用层协议。当我们将客户主机ip地址设置为动态获取方式时,DHCP服务器就会根据DHCP协议给客户端分配IP,使得客户机能够利用这个IP上网。
SW1 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 [SH - HX - SW1 ]ip pool vlan10 gateway- list 10.10 .10.254 network 10.10 .10.0 mask 255.255 .255.0 excluded- ip- address 10.10 .10.129 10.10 .10.253 lease day 2 hour 12 minute 0 dns- list 114.114 .114.114 # ip pool vlan20 gateway- list 10.10 .20.254 network 10.10 .20.0 mask 255.255 .255.0 excluded- ip- address 10.10 .20.129 10.10 .20.253 lease day 2 hour 12 minute 0 dns- list 114.114 .114.114 # ip pool vlan30 gateway- list 10.10 .30.254 network 10.10 .30.0 mask 255.255 .255.0 excluded- ip- address 10.10 .30.3 10.10 .30.128 lease day 2 hour 12 minute 0 dns- list 114.114 .114.114 # ip pool vlan40 gateway- list 10.10 .40.254 network 10.10 .40.0 mask 255.255 .255.0 excluded- ip- address 10.10 .40.3 10.10 .40.128 lease day 2 hour 12 minute 0 dns- list 114.114 .114.114 #
SW2 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 [SH - HX - SW2 ]ip pool vlan10 gateway- list 10.10 .10.254 network 10.10 .10.0 mask 255.255 .255.0 excluded- ip- address 10.10 .10.129 10.10 .10.253 lease day 2 hour 12 minute 0 dns- list 114.114 .114.114 # ip pool vlan20 gateway- list 10.10 .20.254 network 10.10 .20.0 mask 255.255 .255.0 excluded- ip- address 10.10 .20.129 10.10 .20.253 lease day 2 hour 12 minute 0 dns- list 114.114 .114.114 # ip pool vlan30 gateway- list 10.10 .30.254 network 10.10 .30.0 mask 255.255 .255.0 excluded- ip- address 10.10 .30.3 10.10 .30.128 lease day 2 hour 12 minute 0 dns- list 114.114 .114.114 # ip pool vlan40 gateway- list 10.10 .40.254 network 10.10 .40.0 mask 255.255 .255.0 excluded- ip- address 10.10 .40.3 10.10 .40.128 lease day 2 hour 12 minute 0 dns- list 114.114 .114.114 #
SW1 1 2 3 4 5 6 7 8 9 10 [SH - HX - SW1 ]dhcp enable interface Vlanif10 dhcp select global interface Vlanif20 dhcp select global interface Vlanif30 dhcp select global interface Vlanif40 dhcp select global
SW2 1 2 3 4 5 6 7 8 9 10 [SH - HX - SW2 ]dhcp enable interface Vlanif10 dhcp select global interface Vlanif20 dhcp select global interface Vlanif30 dhcp select global interface Vlanif40 dhcp select global
PC 6.OSPF OSPF(Open Shortest Path First 开放式最短路径优先)是一种动态路由协议,属于内部网关协议(Interior Gateway Protocol,简称 IGP),是基于链路状态算法的路由协议。
SW1 1 2 3 4 5 6 7 8 9 [SH - HX - SW1 ]ospf 1 router- id 1.1 .1.1 area 0.0 .0.0 network 10.10 .10.0 0.0 .0.255 network 10.10 .20.0 0.0 .0.255 network 10.10 .30.0 0.0 .0.255 network 10.10 .40.0 0.0 .0.255 network 10.10 .50.0 0.0 .0.255 network 10.10 .60.0 0.0 .0.255 network 10.10 .100.0 0.0 .0.255
SW2 1 2 3 4 5 6 7 8 9 [SH - HX - SW2 ]ospf 1 router- id 2.2 .2.2 area 0.0 .0.0 network 10.10 .10.0 0.0 .0.255 network 10.10 .20.0 0.0 .0.255 network 10.10 .30.0 0.0 .0.255 network 10.10 .40.0 0.0 .0.255 network 10.10 .50.0 0.0 .0.255 network 10.10 .60.0 0.0 .0.255 network 10.10 .200.0 0.0 .0.255
R1 1 2 3 4 [SH - BJ - R1 ]ospf 1 router- id 3.3 .3.3 area 0.0 .0.0 network 10.10 .100.0 0.0 .0.255 network 10.10 .200.0 0.0 .0.255
7.ACL 访问控制列表ACL(Access Control List)是由一条或多条规则组成的集合。所谓规则,是指描述报文匹配条件的判断语句,这些条件可以是报文的源地址、目的地址、端口号等。通过ACL来对报文进行过滤,可以根据业务需求来对这些报文进行允许或阻止的策略。
目的:
防止重要的资源被恶意访问,造成损失。
防止带宽被随意挤占,提高业务的带宽质量。
防止外网的病毒侵入,给内部网络造成安全隐患。
作用:
在流量经过的网络设备的进或出接口上,匹配流量产生允许或拒绝的动作。
定义感兴趣流量,为其他策略或协议提供帮助。
SW1 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 [SH - HX - SW1 ]acl number 3000 rule 5 deny ip source 10.10 .30.0 0.0 .0.255 destination 10.10 .40.0 0.0 .0.255 rule 10 permit ip source 10.10 .30.0 0.0 .0.255 destination 10.10 .10.0 0.0 .0.255 rule 15 permit ip source 10.10 .30.0 0.0 .0.255 destination 10.10 .50.0 0.0 .0.255 rule 20 deny ip source 10.10 .30.0 0.0 .0.255 destination 10.10 .20.0 0.0 .0.255 acl number 3001 rule 5 deny ip source 10.10 .40.0 0.0 .0.255 destination 10.10 .30.0 0.0 .0.255 rule 10 permit ip source 10.10 .40.0 0.0 .0.255 destination 10.10 .10.0 0.0 .0.255 rule 15 permit ip source 10.10 .40.0 0.0 .0.255 destination 10.10 .50.0 0.0 .0.255 rule 20 deny ip source 10.10 .40.0 0.0 .0.255 destination 10.10 .20.0 0.0 .0.255 acl number 3002 rule 5 permit ip source 10.10 .20.0 0.0 .0.255 destination 10.10 .10.0 0.0 .0.255 rule 10 permit ip source 10.10 .20.0 0.0 .0.255 destination 10.10 .50.0 0.0 .0.255 rule 15 deny ip source 10.10 .20.0 0.0 .0.255 destination 10.10 .30.0 0.0 .0.255 rule 20 deny ip source 10.10 .20.0 0.0 .0.255 destination 10.10 .40.0 0.0 .0.255
SW2 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 [SH - HX - SW2 ]acl number 3000 rule 5 deny ip source 10.10 .30.0 0.0 .0.255 destination 10.10 .40.0 0.0 .0.255 rule 10 permit ip source 10.10 .30.0 0.0 .0.255 destination 10.10 .10.0 0.0 .0.255 rule 15 permit ip source 10.10 .30.0 0.0 .0.255 destination 10.10 .50.0 0.0 .0.255 rule 20 deny ip source 10.10 .30.0 0.0 .0.255 destination 10.10 .20.0 0.0 .0.255 acl number 3001 rule 5 deny ip source 10.10 .40.0 0.0 .0.255 destination 10.10 .30.0 0.0 .0.255 rule 10 permit ip source 10.10 .40.0 0.0 .0.255 destination 10.10 .10.0 0.0 .0.255 rule 15 permit ip source 10.10 .40.0 0.0 .0.255 destination 10.10 .50.0 0.0 .0.255 rule 20 deny ip source 10.10 .40.0 0.0 .0.255 destination 10.10 .20.0 0.0 .0.255 acl number 3002 rule 5 permit ip source 10.10 .20.0 0.0 .0.255 destination 10.10 .10.0 0.0 .0.255 rule 10 permit ip source 10.10 .20.0 0.0 .0.255 destination 10.10 .50.0 0.0 .0.255 rule 15 deny ip source 10.10 .20.0 0.0 .0.255 destination 10.10 .30.0 0.0 .0.255 rule 20 deny ip source 10.10 .20.0 0.0 .0.255 destination 10.10 .40.0 0.0 .0.255
SW1 1 2 3 4 5 [SH - HX - SW1 ]interface GigabitEthernet0 / 0 / 3 traffic- filter inbound acl 3000 traffic- filter inbound acl 3001 traffic- filter inbound acl 3002
SW2 1 2 3 4 5 [SH - HX - SW2 ]interface GigabitEthernet0 / 0 / 3 traffic- filter inbound acl 3000 traffic- filter inbound acl 3001 traffic- filter inbound acl 3002
8.NAT 通过在出口路由上做NAT,使内网访问外网通过出口路由时,源地址会转换成特定公有地址,并且将两个ip映射关系加到NAT映射表上。
在外网向内网通信时,目的地址还是特定公有地址,但是到达出口路由器后,查看NAT映射表,从而转换为私有地址。
R1 1 2 3 4 5 6 7 8 9 10 11 12 13 [SH - BJ - R1 ]nat static global 200.200 .200.3 inside 10.10 .50.1 netmask 255.255 .255.255 [SH - BJ - R1 ]ip route- static 0.0 .0.0 0.0 .0.0 200.200 .200.1 ip route- static 10.10 .0.0 255.255 .0.0 10.10 .100.2 [SH - BJ - R1 ]ospf 1 import -route static [SH - WW - R2 ]ip route- static 0.0 .0.0 0.0 .0.0 200.200 .200.2
R2其他配置 1 2 3 4 5 [SH - WW - R2 ]interface Ethernet0 / 0 / 0 ip address 9.9 .9.254 255.255 .255.0 # interface Ethernet0 / 0 / 1 ip address 8.8 .8.254 255.255 .255.0
PC6与客户端 1 2 3 4 5 6 7 8 9 PC6 IP : 9.9 .9.9 mask: 255.255 .255.0 Gateway : 9.9 .9.254 Client IP:8 .8.8 .8 mask: 255.255 .255.0 Gateway : 8.8 .8.254